White Paper Excerpt – Opportunities Today
Wi-Fi and Cellular Convergence
Business and technical consolidation trends all point in the same direction: Mobile and fixed networks are coming together – for the benefit of everyone in the industry and consumers.
5G introduces new network architectural concepts for Wi-Fi integration with the mobile core (non-3GPP access). In this post, we first explore the opportunities for mobile operators today and then the basic concepts of trusted and untrusted Wi-Fi access. In our next blog post about Wi-Fi and Cellular convergence, we will dive into what is new within 5G, introduced in 3GPP releases 15 and 16. After that blog post, we will cover the new Access Traffic Steering, Switching & Splitting (ATSSS) function, the ‘Holy Grail’ of mobile data offloading. Spoiler alert; ATSSS complexity and reliance on device support mean it will likely take years to come to market.
Wi-Fi in the 5G era – White Paper
This is an excerpt from our white paper Wi-Fi in the 5G Era – Strategy Guide for Operators. The full white paper is available here if you like what you read. Don’t hesitate to contact us if you have any questions.

While Wi-Fi and cellular are on a gradual path to technical convergence, there can be no question that corporate fixed-cellular convergence, aka consolidation, has already been happening for a long time. Some years ago, dominant mobile operators trended towards acquiring cable and fiber operations. More recently, fixed service providers and cablecos have either acquired mobile operators or have become MVNOs themselves.
All of this is seeding the ground for technology and services convergence in addition to the more apparent corporate consolidation.
But, as already discussed in one of our blog posts, if genuine technical Wi-Fi and mobile (5G) convergence are to happen, service providers also need to break free from conventional organizational ‘silos’ and compartmentalized thinking on what technologies do and do not belong to mobile and fixed wireless services, respectively.
We believe there is significant untapped business potential in breaking such operator ‘silos’ to achieve progress in service and technological convergence.
Some of these opportunities do not need significant infrastructure investments, nor do operators need to wait for new convergence (3GPP) standards or equipment to emerge.
Selective Wi-Fi Offload is the answer
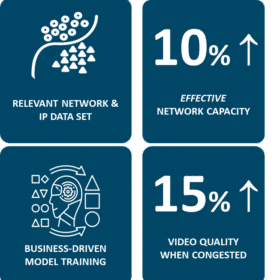
Mobile network traffic data may indicate overcapacity. But that is often only true as a high-level average. There will always be some cell sites suffering from congestion and some only serving a handful of subscribers. Selective Wi-Fi offload is the answer: Build Wi-Fi capacity where it is needed most to make users happy (Churn zone) and always for indoor coverage.
If regulations allow it, mobile operators may even take the bold step to replace cellular with Wi-Fi at some locations (CAPEX overload zone).
Here is our suggested list of reasonably simple network changes that would create a ‘Wi-Fi offload’ service and hence a quick new source of revenue for operators:
- Create an additional SSID (network name) supporting the 802.1x protocol on all of your existing Wi-Fi footprint.
- Enable SIM-based Wi-Fi services authentication (using the EAP-SIM/AKA protocol).
- Introduce selective offloading of mobile traffic to Wi-Fi at various locations.
By introducing the correct configurations and by provisioning devices correctly, such a scheme would create an additional layer of mobile network capacity using Wi-Fi. But this would also require that mobile and fixed parts of the operator organization collaborate.
Let’s now look into how to integrate Wi-Fi with the mobile core. The 3GPP standard offers two main strategies to integrate Wi-Fi networks with the mobile core: Trusted and untrusted non-3GPP (Wi-Fi) access.
Untrusted Non-3GPP (Wi-Fi) Access
Untrusted non-3GPP (Wi-Fi) access was first introduced in the Wi-Fi specification in 3GPP Release 6 (2005). At that time, Wi-Fi access points featuring advanced security features were rare. Hence Wi-Fi was considered open and unsecured by default. Untrusted access includes any Wi-Fi access that the operator has no control over, such as public hotspots, subscribers’ home Wi-Fi, and corporate Wi-Fi. It also consists of Wi-Fi that does not provide sufficient security mechanisms such as authentication and radio link encryption.
The fact that untrusted non-3GPP access works over any Wi-Fi network is the reason that it is the method of choice for Wi-Fi Calling.
The untrusted model requires no changes to the Wi-Fi network but impacts the device side because it needs an IPsec client to reside on the device. The device is connected through a secure IPsec tunnel directly to an IPsec Terminating Gateway in the Mobile Core, which is connected through an encrypted tunnel to the Packet Gateway. The Packet Gateway is used for both cellular and Wi-Fi traffic.
This integration on the core network side also means that Wi-Fi service management platforms, such as the Enea Aptilo Service Management Platform™ (SMP), must interface with mobile core network HLR/HSS/AMF for SIM Authentication (EAP-SIM/AKA/AKA’ or 5G-AKA). This provides the same level of authentication security as in the cellular network. It may also be required to interface with mobile core network policy functions. In addition to authentication of the device, the SIM authentication process produces cryptographic keys used for IPsec tunnel establishment.
Trusted Non-3GPP (Wi-Fi) Access
Trusted non-3GPP (Wi-Fi) access was first introduced with the LTE standard in 3GPP Release 8 (2008). Trusted access is often assumed to be operator-built Wi-Fi access with encryption (enabled by 802.1x) in the Wi-Fi radio access network (RAN) and a secure authentication method (EAP). However, it is always up to the home operator to decide what is considered trusted.
In the case of trusted access, the device (UE) is connected through a Wireless Access Gateway in the Wi-Fi core. This Wireless Access Gateway is connected through a secure tunnel directly with the Packet Gateway, also used for cellular traffic in the Mobile Core.
SIM Authentication is also essential for trusted non-3GPP access. In addition to authentication of the device, it produces cryptographic keys used for encryption in the secure Wi-Fi network (802.1x).